First AutoRecon to map the ports/services
➜ Heist sudo ~/tools/AutoRecon/src/autorecon/autorecon.py 10.10.10.149
[*] Scanning target 10.10.10.149
[*] Running service detection nmap-full-tcp on 10.10.10.149
[*] Running service detection nmap-quick on 10.10.10.149
[*] Running service detection nmap-top-20-udp on 10.10.10.149
[*] [11:55:11] - There are 3 tasks still running on 10.10.10.149
[*] Service detection nmap-quick on 10.10.10.149 finished successfully in 1 minute, 41 seconds
[*] Found http on tcp/80 on target 10.10.10.149
[*] Found msrpc on tcp/135 on target 10.10.10.149
[*] Found microsoft-ds on tcp/445 on target 10.10.10.149
[!] [tcp/445/nbtscan] Scan cannot be run against tcp port 445. Skipping.
[*] Running task tcp/80/sslscan on 10.10.10.149
[*] Running task tcp/80/nmap-http on 10.10.10.149
[*] Running task tcp/80/curl-index on 10.10.10.149
[*] Running task tcp/80/curl-robots on 10.10.10.149
[*] Running task tcp/80/wkhtmltoimage on 10.10.10.149
[*] Running task tcp/80/whatweb on 10.10.10.149
[*] Running task tcp/80/ffuf on 10.10.10.149
[*] Running task tcp/135/sslscan on 10.10.10.149
[*] Task tcp/80/sslscan on 10.10.10.149 finished successfully in less than a second
[*] Task tcp/80/wkhtmltoimage on 10.10.10.149 finished successfully in less than a second
[*] Running task tcp/135/nmap-msrpc on 10.10.10.149
[*] Running task tcp/445/sslscan on 10.10.10.149
[*] Task tcp/135/sslscan on 10.10.10.149 finished successfully in less than a second
[*] Running task tcp/445/nmap-smb on 10.10.10.149
[*] Task tcp/445/sslscan on 10.10.10.149 finished successfully in less than a second
[*] Running task tcp/445/enum4linux on 10.10.10.149
[*] Task tcp/80/ffuf on 10.10.10.149 finished successfully in less than a second
[*] Running task tcp/445/smbclient on 10.10.10.149
[*] Task tcp/445/enum4linux on 10.10.10.149 finished successfully in less than a second
[*] Running task tcp/445/smbmap-share-permissions on 10.10.10.149
[*] Task tcp/445/smbclient on 10.10.10.149 finished successfully in less than a second
[*] Task tcp/80/curl-index on 10.10.10.149 finished successfully in less than a second
[*] Running task tcp/445/smbmap-list-contents on 10.10.10.149
[*] Running task tcp/445/smbmap-execute-command on 10.10.10.149
[*] Task tcp/445/smbmap-share-permissions on 10.10.10.149 finished successfully in less than a second
[*] Task tcp/80/curl-robots on 10.10.10.149 finished successfully in less than a second
[*] Task tcp/445/smbmap-execute-command on 10.10.10.149 finished successfully in less than a second
[*] Task tcp/445/smbmap-list-contents on 10.10.10.149 finished successfully in less than a second
[*] Task tcp/80/whatweb on 10.10.10.149 finished successfully in 14 seconds
[*] [11:56:11] - There are 5 tasks still running on 10.10.10.149
[*] Task tcp/135/nmap-msrpc on 10.10.10.149 finished successfully in 23 seconds
[*] Task tcp/445/nmap-smb on 10.10.10.149 finished successfully in 49 seconds
[*] [11:57:11] - There are 3 tasks still running on 10.10.10.149
[*] Service detection nmap-full-tcp on 10.10.10.149 finished successfully in 3 minutes, 35 seconds
[*] Found http on tcp/5985 on target 10.10.10.149
[*] Found msrpc on tcp/49669 on target 10.10.10.149
[*] Running task tcp/5985/sslscan on 10.10.10.149
[*] Running task tcp/5985/nmap-http on 10.10.10.149
[*] Running task tcp/5985/curl-index on 10.10.10.149
[*] Running task tcp/5985/curl-robots on 10.10.10.149
[*] Running task tcp/5985/wkhtmltoimage on 10.10.10.149
[*] Running task tcp/5985/whatweb on 10.10.10.149
[*] Running task tcp/5985/ffuf on 10.10.10.149
[*] Running task tcp/49669/sslscan on 10.10.10.149
[*] Task tcp/5985/sslscan on 10.10.10.149 finished successfully in less than a second
[*] Task tcp/5985/wkhtmltoimage on 10.10.10.149 finished successfully in less than a second
[*] Running task tcp/49669/nmap-msrpc on 10.10.10.149
[*] Task tcp/49669/sslscan on 10.10.10.149 finished successfully in less than a second
[*] Task tcp/5985/ffuf on 10.10.10.149 finished successfully in less than a second
[*] Task tcp/5985/curl-index on 10.10.10.149 finished successfully in less than a second
[*] Task tcp/5985/curl-robots on 10.10.10.149 finished successfully in less than a second
[*] Task tcp/5985/whatweb on 10.10.10.149 finished successfully in 6 seconds
[*] [11:58:11] - There are 4 tasks still running on 10.10.10.149
[*] Task tcp/80/nmap-http on 10.10.10.149 finished successfully in 3 minutes, 2 seconds
[*] Task tcp/49669/nmap-msrpc on 10.10.10.149 finished successfully in 1 minute, 11 seconds
[*] [11:59:11] - There are 2 tasks still running on 10.10.10.149
[*] [12:00:11] - There are 2 tasks still running on 10.10.10.149
[*] [12:01:11] - There are 2 tasks still running on 10.10.10.149
[*] [12:02:11] - There are 2 tasks still running on 10.10.10.149
[*] Task tcp/5985/nmap-http on 10.10.10.149 finished successfully in 5 minutes, 2 seconds
[*] Service detection nmap-top-20-udp on 10.10.10.149 finished successfully in 8 minutes, 58 seconds
[*] Finished scanning target 10.10.10.149 in 8 minutes, 58 seconds
[*] Finished scanning all targets in 8 minutes, 58 seconds!
Nmap Full TCP results
Nmap scan report for 10.10.10.149
Host is up, received user-set (0.064s latency).
Scanned at 2021-04-15 11:54:12 CEST for 214s
Not shown: 65530 filtered tcp ports (no-response)
PORT STATE SERVICE REASON VERSION
80/tcp open http syn-ack ttl 127 Microsoft IIS httpd 10.0
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
| http-title: Support Login Page
|_Requested resource was login.php
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
445/tcp open microsoft-ds? syn-ack ttl 127
5985/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49669/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
OS fingerprint not ideal because: Missing a closed TCP port so results incomplete
No OS matches for host
TCP/IP fingerprint:
SCAN(V=7.91SVN%E=4%D=4/15%OT=80%CT=%CU=%PV=Y%DS=2%DC=T%G=N%TM=60780E1A%P=x86_64-unknown-linux-gnu)
SEQ(SP=105%GCD=1%ISR=10E%TI=I%II=I%SS=S%TS=U)
OPS(O1=M54DNW8NNS%O2=M54DNW8NNS%O3=M54DNW8%O4=M54DNW8NNS%O5=M54DNW8NNS%O6=M54DNNS)
WIN(W1=FFFF%W2=FFFF%W3=FFFF%W4=FFFF%W5=FFFF%W6=FF70)
ECN(R=Y%DF=Y%TG=80%W=FFFF%O=M54DNW8NNS%CC=Y%Q=)
T1(R=Y%DF=Y%TG=80%S=O%A=S+%F=AS%RD=0%Q=)
T2(R=N)
T3(R=N)
T4(R=N)
U1(R=N)
IE(R=Y%DFI=N%TG=80%CD=Z)
Network Distance: 2 hops
TCP Sequence Prediction: Difficulty=260 (Good luck!)
IP ID Sequence Generation: Incremental
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: 10m01s
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 17094/tcp): CLEAN (Timeout)
| Check 2 (port 48515/tcp): CLEAN (Timeout)
| Check 3 (port 25486/udp): CLEAN (Timeout)
| Check 4 (port 43360/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled but not required
| smb2-time:
| date: 2021-04-15T10:07:11
|_ start_date: N/A
TRACEROUTE (using port 445/tcp)
HOP RTT ADDRESS
1 67.50 ms 10.10.14.1
2 67.45 ms 10.10.10.149
Read data files from: /usr/local/bin/../share/nmap
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Thu Apr 15 11:57:46 2021 -- 1 IP address (1 host up) scanned in 215.03 seconds
Nikto results:
nikto -ask=no -h http://10.10.10.149:80 2>&1 | tee "/home/lillox/Desktop/HTB/Heist/results/10.10.10.149/scans/tcp_80_http_nikto.txt"
tee: /home/lillox/Desktop/HTB/Heist/results/10.10.10.149/scans/tcp_80_http_nikto.txt: Permission denied
- Nikto v2.1.6
---------------------------------------------------------------------------
+ Target IP: 10.10.10.149
+ Target Hostname: 10.10.10.149
+ Target Port: 80
+ Start Time: 2021-04-15 14:11:49 (GMT2)
---------------------------------------------------------------------------
+ Server: Microsoft-IIS/10.0
+ Retrieved x-powered-by header: PHP/7.3.1
+ The anti-clickjacking X-Frame-Options header is not present.
+ The X-XSS-Protection header is not defined. This header can hint to the user agent to protect against some forms of XSS
+ The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type
+ Cookie PHPSESSID created without the httponly flag
+ Root page / redirects to: login.php
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ Allowed HTTP Methods: OPTIONS, TRACE, GET, HEAD, POST
+ Public HTTP Methods: OPTIONS, TRACE, GET, HEAD, POST
+ /login.php: Admin login page/section found.
+ 7863 requests: 0 error(s) and 8 item(s) reported on remote host
+ End Time: 2021-04-15 14:22:23 (GMT2) (634 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
WhatWeb results:
WhatWeb report for http://10.10.10.149:80
Status : 302 Found
Title : <None>
IP : 10.10.10.149
Country : RESERVED, ZZ
Summary : Microsoft-IIS[10.0], HTTPServer[Microsoft-IIS/10.0], X-Powered-By[PHP/7.3.1], Cookies[PHPSESSID], PHP[7.3.1], RedirectLocation[login.php]
Detected Plugins:
[ Cookies ]
Display the names of cookies in the HTTP headers. The
values are not returned to save on space.
String : PHPSESSID
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
String : Microsoft-IIS/10.0 (from server string)
[ Microsoft-IIS ]
Microsoft Internet Information Services (IIS) for Windows
Server is a flexible, secure and easy-to-manage Web server
for hosting anything on the Web. From media streaming to
web application hosting, IIS's scalable and open
architecture is ready to handle the most demanding tasks.
Version : 10.0
Website : http://www.iis.net/
[ PHP ]
PHP is a widely-used general-purpose scripting language
that is especially suited for Web development and can be
embedded into HTML. This plugin identifies PHP errors,
modules and versions and extracts the local file path and
username if present.
Version : 7.3.1
Google Dorks: (2)
Website : http://www.php.net/
[ RedirectLocation ]
HTTP Server string location. used with http-status 301 and
302
String : login.php (from location)
[ X-Powered-By ]
X-Powered-By HTTP header
String : PHP/7.3.1 (from x-powered-by string)
HTTP Headers:
HTTP/1.1 302 Found
Cache-Control: no-store, no-cache, must-revalidate
Pragma: no-cache
Content-Type: text/html; charset=UTF-8
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Location: login.php
Server: Microsoft-IIS/10.0
X-Powered-By: PHP/7.3.1
Set-Cookie: PHPSESSID=3vehdk0gmnrcsl9fcnm0elmvfv; path=/
Date: Thu, 15 Apr 2021 12:13:29 GMT
Connection: close
Content-Length: 0
➜ scans /home/lillox/tools/dirsearch/dirsearch.py -u http://10.10.10.149 -e php,ini,bck,js
_|. _ _ _ _ _ _|_ v0.4.1
(_||| _) (/_(_|| (_| )
Extensions: php, ini, bck, js | HTTP method: GET | Threads: 30 | Wordlist size: 10390
Error Log: /home/lillox/tools/dirsearch/logs/errors-21-04-15_16-31-40.log
Target: http://10.10.10.149/
Output File: /home/lillox/tools/dirsearch/reports/10.10.10.149/_21-04-15_16-31-40.txt
[16:31:40] Starting:
[16:31:41] 301 - 146B - /js -> http://10.10.10.149/js/
[16:31:41] 403 - 312B - /%2e%2e//google.com
[16:31:48] 403 - 312B - /\..\..\..\..\..\..\..\..\..\etc\passwd
[16:31:53] 301 - 155B - /attachments -> http://10.10.10.149/attachments/
[16:31:56] 301 - 147B - /css -> http://10.10.10.149/css/
[16:31:58] 200 - 1KB - /errorpage.php
[16:31:59] 403 - 1KB - /images/
[16:31:59] 301 - 150B - /images -> http://10.10.10.149/images/
[16:32:00] 302 - 0B - /index.php -> login.php
[16:32:00] 302 - 0B - /index.php/login/ -> login.php
[16:32:00] 403 - 1KB - /js/
[16:32:01] 200 - 2KB - /login.php
Task Completed
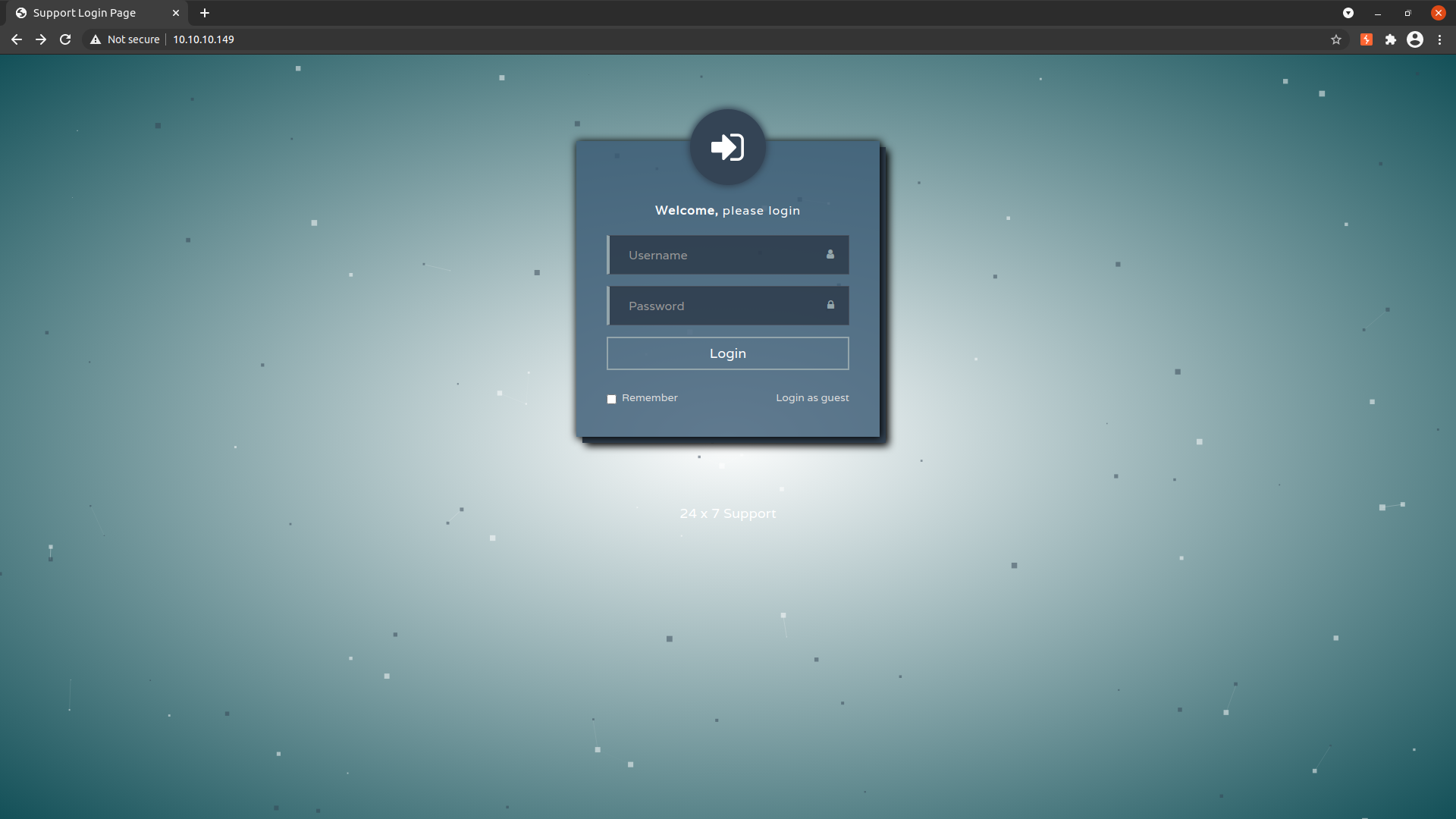
The web site on the port 80 offers a login prompt: